Summary :
This article discusses the procedure to upload a CA signed certificate to PMP/PTP 450x radios for HTTPS access.
Cause :
When the user tries to login to a radio through HTTPS, an invalid certificate warning is issued. A CA signed certificate can help overcome this issue and secure the network. However, the certificate needs to be converted to PKCS#12 format file (Cert + private key) format to be accepted the radio
Solution: Convert the CA signed certificate to .pfx format
Requirements
- The original private key used for the certificate
- A PEM (.pem, .crt, .cer) or PKCS#7/P7B (.p7b, .p7c) File
- OpenSSL(/index.html (openssl.org)) (included with Linux/Unix and macOS, and easily installed on Windows with Cygwin(Install OpenSSL on Windows with Cygwin - SSL.com))
By default, the conversion of cert/key to PKCS#12 by openssl using RC2-40 algorithm, which is not supported by PMP450x products.
The commands below demonstrate examples of how to create a .pfx/.p12 file in the command line using OpenSSL:
Source certificate from PEM (.pem, .crt, .cer) to PFX
openssl pkcs12 -export -certpbe PBE-SHA1-3DES -out certificate.pfx -inkey privateKey.key -in certificate.crt
Breaking down the command:
openssl – the command for executing OpenSSL
pkcs12 – the file utility for PKCS#12 files in OpenSSL
-export -certpbe PBE-SHA1-3DES -out certificate.pfx – export and save the PFX file as certificate.pfx with SHA1 algorithm
-inkey privateKey.key – use the private key file privateKey.key as the private key to combine with the certificate.
-in certificate.crt – use certificate.crt as the certificate the private key will be combined with.
NOTE: After entering the command, you will be prompted to enter and verify an export password to protect the PFX file. Remember this password! You will need it when you wish to export the certificates and key.
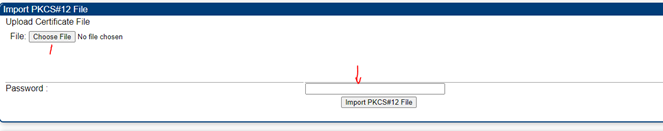
Once the PFX file is generated, it can be imported to the device under configuration>>security
Once the import is done, it will ask to reboot the PMP450, after reboot, you should see the imported certificate, like the following.

Reference: Create a .pfx/.p12 Certificate File Using OpenSSL - SSL.com