Overview:
This documents provides information about configuring Active directory settings on Windows platform for cnMaestro user authentication.
Pre-requisites:
Windows Server 2012R2 with Active Directory installed.
Configuration: The steps below configure cnMaestro for administration account authentication using Active Directory as the primary authenticator (the local user database will become secondary).
Step1: Adding new Organisational unit
- Navigate to Administrative Tools > Active Directory Users and Computers
- Right click on domain and create new Organisational unit.
Step 2: Adding groups under Organisational unit
- Select the Organisational unit.
- Right click and select Group.
- Add a group name with default setting as shown in below picture.

Note: Create four groups for each role (super-admin, admin, operator, and monitor). Group names should be unique with allowable characters.
Step 3: Adding Users under Organisational unit.
- Select the Organisational Unit.
- Right click and create new user.
- Fill user details, click next and create password.
- Finally submit to create a user


Note: Create multiple users with unique names
Step 4: Mapping the users with groups
- Right click on the user and select properties.
- Select Member Of and click Add option.
- Select Groups option will pop up.
- Type the group name to which the user should be mapped and click Ok.
- Map all the users to required groups.
Note: users should be uniquely mapped to groups, and one user cannot exist in multiple groups.
Step 5: cnMaestro Configuration
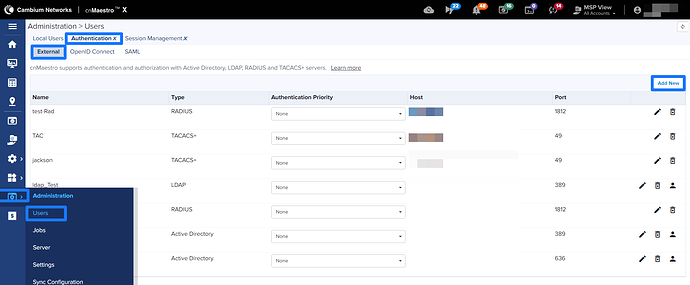
- Navigate to Administration > Users and click on Authentication > External > Add New in the cnMaestro On-Premises UI to create the Active directory entry.
- Configure the Authentication Server Name, Select Authentication Server Type as Active Directory , Active Directory Server IP address and Base DN values.
Note: If SSL/TLS Security is enabled, upload a root certificate of Active Directory server and provide Hostname under IP Address/Hostname column instead of IP Address.
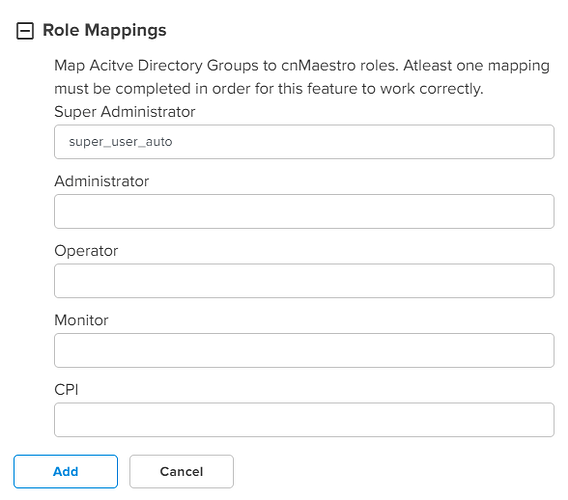
- Enter the group names that are created previously in Active Directory server as per requirement under Role Mappings.
For ex: If a group name “super_user_auto” is created in Active directory server, enter the same group name in Super Administrator field. Fill the other group names under remaining fields.
- The users under this groups will be differentiated based up on the Role Mappings.
- Click on Add button to add the Active Directory Server.
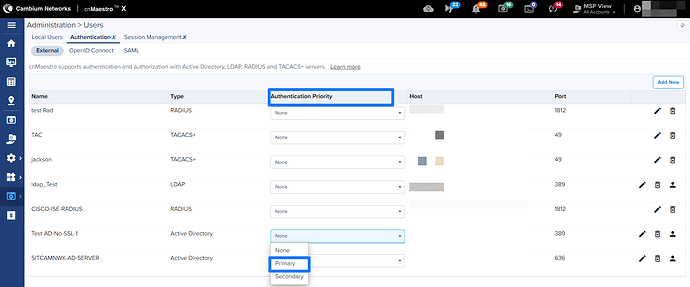
Navigate to Adminstration > Users and click on Authentication > External and set the Authentication Priority to Primary for the Active Directory server created.
The Secondary Authentication will be automatically set to Local Users, which means if the Active Directory server is not reachable, the UI can be accessed using the Local Users database (so it is important to change the default password). If you are unable to log into the UI, you can create a One-Time password in the CLI in order to resolve the issue. (see the User Guide for details on Application Account Recovery.
Note: Use complete user name with domain name to login to cnMaestro as cnMaestro will not do Bind DN to user name.