The HTTPS protocol relies on the web server providing a signed security certificate to the web browser. The web browser checks the certificate by attempting to assemble a chain of certificates starting with the web server and culminating in a Root CA certificate from its store of trusted certificates. Root CA certificates for the well-known CAs are included as part of the operating system or are added automatically when a new browser is installed.
In PTP 500/600/650/670/700, the ODU is the web server, and your management computer hosts the browser. The certificate for the ODU must have the ODU’s IP address as the subject, and this prevents us from using certificates signed by the well known CAs like Comodo. This means that you need to sign your own certificates, and you will need to add the associated Root CA certificate to the browser.
Note that the Root CA certificate is not in any way a secret. The crucial thing is that the browser must be able to locate the certificate in its store of trusted certificates. Google Chrome uses the standard Windows certificate store. Add a Root CA certificate to the certificate store like this:
Open the Root CA certificate by double-clicking:
Click Install Certificate…
Select Local Machine and click Next.
Select Place all certificates in the following store. Browse and select Trusted Root Certification Authorities as the store. Click Next.
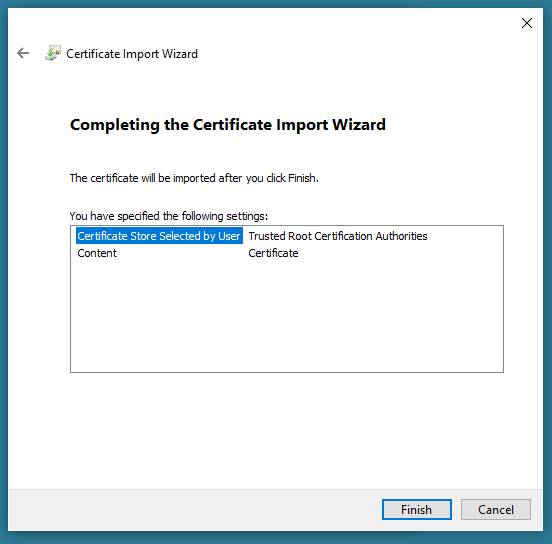
Click Finish.
If this all went as it should, you’ll see this dialog:

When you navigate to the ODU web-based management using HTTPS, you should see the padlock icon like this: